Litecoin Reverses 13 Blocks After Exploit as Patch History Faces Scrutiny
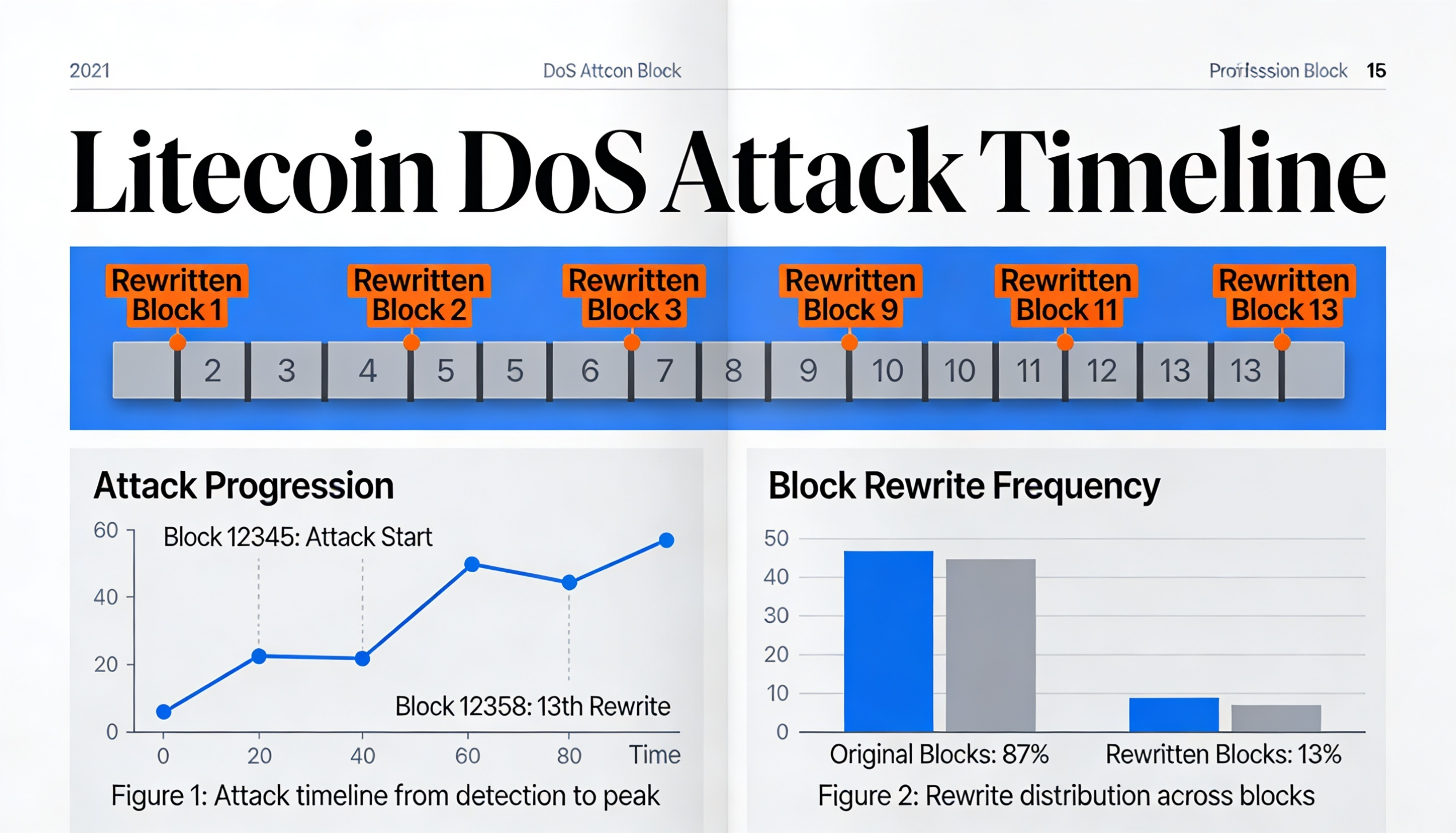
Litecoin rolled back 13 blocks late Friday into Saturday, undoing roughly half an hour of transactions after attackers exploited a flaw in its Mimblewimble Extension Block (MWEB) protocol.
The vulnerability allowed invalid MWEB transactions to be accepted by nodes running outdated software, enabling a denial-of-service (DoS) attack that disrupted major mining pools. The network corrected the issue by switching back to the longest valid chain.
The Litecoin Foundation labeled the incident a zero-day exploit and said Sunday that the issue had been fully resolved, with the network operating normally.
However, publicly available GitHub data suggests the underlying flaw had been identified and quietly fixed weeks earlier. Security researcher “bbsz” of the SEAL911 response group noted that the consensus vulnerability tied to invalid MWEB peg-out transactions was patched between March 19 and March 26.
A separate DoS vulnerability was addressed on April 25, and both fixes were later included in release 0.21.5.4 — after the attack had already begun.
This sequence indicates the vulnerability had been resolved in code but not widely deployed across the network in time, leaving some nodes and mining pools exposed.
The incident highlights a recurring issue in decentralized systems: even when critical bugs are patched, delays in adoption can create windows for exploitation.